Types of DoS Attacks
Denial of Service (DoS) attacks have evolved into one of the most disruptive forms of cyber threats in the modern digital landscape. By overwhelming a system, network, or application with excessive traffic or requests, attackers aim to render resources unavailable to legitimate users. Understanding the types of DoS attacks is essential for organizations, cybersecurity teams, and IT professionals who want to build robust protection strategies.
This article provides a detailed, academically structured overview of the most common DoS attack types, how they function, why they are dangerous, and how organizations can detect and prevent them. Whether you are a beginner in cybersecurity or an advanced learner, this guide will give you a clear understanding of the mechanisms behind various DoS techniques.
Read: Security Risks of Cloud Computing
What Is a DoS Attack?
A Denial of Service attack is a malicious attempt to shut down a system or degrade its performance by exhausting critical resources such as bandwidth, memory, or CPU power. Unlike Distributed Denial of Service (DDoS) attacks—which involve multiple machines—DoS attacks typically originate from a single source. Despite this, they can still cause significant damage to businesses, online platforms, and cloud-based services.
Why Understanding DoS Attack Types Matters
DoS attacks vary in their techniques, entry points, and impact. Identifying different types of DoS attacks helps organizations:
Build accurate incident-response strategies
Deploy appropriate network security tools
Strengthen firewalls and load balancers
Reduce downtime and financial losses
Improve cloud and infrastructure resilience
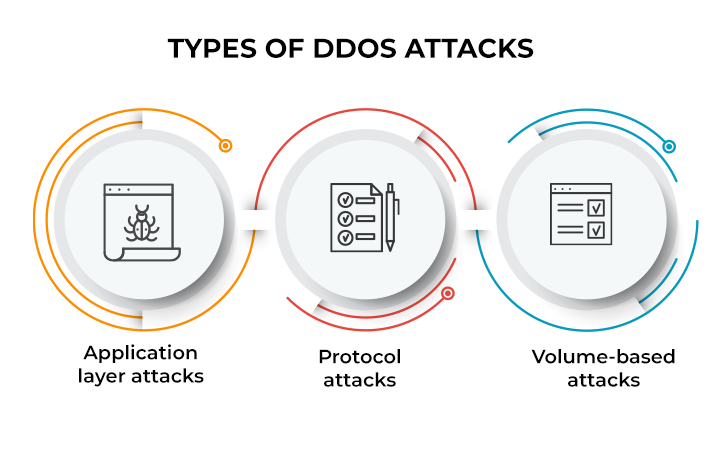
Types of DoS Attacks
Below is a comprehensive, well-structured breakdown of the most important types of DoS attacks, each with its mechanism, impact, and examples.
1. Volume-Based DoS Attacks
Volume-based attacks consume network bandwidth by sending massive amounts of traffic to a target system. They are the most common type of DoS attacks.
1.1 UDP Flood Attack
A UDP flood bombards the victim’s server with User Datagram Protocol packets. Because UDP is connectionless, the server attempts to respond to each packet, eventually exhausting resources.
Target: Ports and network interfaces
Impact: Network congestion and connection failures
Key characteristic: High volume, low complexity
1.2 ICMP Flood (Ping Flood)
This attack works by sending ICMP Echo Request packets (pings) to the target at a very high rate. The target tries to respond to each one, eventually becoming overwhelmed.
Target: Bandwidth and CPU
Impact: Slow connection, packet loss, downtime
Common in: Poorly protected servers
1.3 Ping of Death
The Ping of Death sends oversized ping packets that exceed the maximum allowed IP packet size (65,535 bytes). This causes system crashes or reboots.
Target: Older operating systems
Impact: System freeze or crash
Note: Modern systems are mostly patched
Types of DoS Attacks
2. Protocol-Based DoS Attacks
These attacks exploit weaknesses in network protocols such as TCP, ICMP, and HTTP.
2.1 SYN Flood Attack
A SYN Flood targets the TCP handshake process. The attacker sends repeated SYN requests without completing the handshake, leaving the server with half-open connections until it can no longer accept new connections.
Target: TCP resources
Impact: Connection timeouts, application downtime
Common mitigation: SYN cookies, firewalls
2.2 Smurf Attack
A Smurf attack uses ICMP requests sent to a broadcast network address, amplifying the traffic and overwhelming the victim.
Mechanism: Reflection + amplification
Impact: Network saturation
Prevention: Disable directed broadcast
2.3 Fragmentation Attack (Teardrop)
Fragmentation attacks send overlapping or incorrectly sized packet fragments, which confuse systems during reassembly.
Target: OS kernel
Impact: System crash or freeze
Modern OS: Usually protected
Types of DoS Attacks
3. Application-Layer DoS Attacks
Application-layer DoS attacks target the top layer of the OSI model, focusing on applications like web servers, APIs, or databases.
3.1 HTTP Flood Attack
This attack sends a massive number of HTTP GET or POST requests to a web server, consuming CPU and memory.
Target: Web applications
Impact: Server overload and page unavailability
Hard to detect: Appears like normal traffic
3.2 Slowloris Attack
Slowloris sends partial HTTP requests and keeps connections open as long as possible. The server waits for the rest of the request until it runs out of available connections.
Impact: Server resource exhaustion
Key characteristic: Low bandwidth, high damage
Vulnerable: Apache-based servers
3.3 DNS Query Flood
The attacker sends high volumes of DNS lookup requests, overwhelming DNS servers.
Impact: Domain unavailability
Risk: Email, website, and API downtime
Target: DNS resolvers
Types of DoS Attacks
4. Logic-Based DoS Attacks
These attacks exploit software bugs, system design flaws, or misconfigurations.
4.1 Buffer Overflow Attack
Attackers send more data into a buffer than it can handle, causing:
System crashes
Unpredictable behavior
Potential remote code execution
4.2 Zero-Day DoS Attacks
Zero-day DoS attacks exploit vulnerabilities that have not yet been patched.
Impact: High risk
Defensive challenge: No prior knowledge
Targets: Applications, operating systems, IoT devices
4.3 Misconfiguration Exploitation
Systems that are improperly configured—such as open ports, outdated firmware, or weak firewall rules—enable attackers to overload resources easily.
Types of DoS Attacks
5. Distributed DoS (DDoS) vs. DoS: The Overlap
While this article focuses on DoS, many attack types have DDoS variants. In DDoS attacks, thousands of compromised devices (botnets) execute the attack. The techniques are similar, but the scale is exponentially larger.
Examples include:
DDoS SYN Flood
DNS Amplification DDoS
HTTP Flood DDoS
How to Detect DoS Attacks
Organizations can use the following tools and techniques:
Network monitoring systems
Firewall and IDS/IPS logs
Anomaly detection tools
Rate-limiting systems
Cloud-based DDoS protection like AWS Shield or Cloudflare
Common signs include:
Slow system performance
Unusual traffic spikes
Service timeouts
High CPU or bandwidth usage
Repeated requests from a single IP
How to Prevent DoS Attacks
1. Firewalls and Access Control Lists (ACLs)
Block malicious traffic patterns.
2. Rate Limiting
Restricts excessive requests from a single user.
3. Load Balancing
Distributes traffic across multiple servers.
4. Web Application Firewalls (WAF)
Protects against HTTP-level attacks.
5. Cloud-Based DDoS Protection
Such as Cloudflare, Akamai, or AWS Shield.
6. Patch Management
Fixes vulnerabilities that may be exploited.
7. Redundant Architecture
Multiple servers and networks reduce single-point failures.
Types of DoS Attacks
Conclusion
Understanding the types of DoS attacks is crucial for protecting digital environments from performance degradation, downtime, and financial loss. From volume-based floods to application-layer attacks and protocol exploitation, DoS threats continue to evolve in complexity. Implementing strong security controls—firewalls, rate limiting, DDoS protection, and continuous monitoring—can significantly reduce risk.
With cyber threats increasing globally, a proactive approach to identifying DoS attack types and understanding how they operate is essential for every modern business.