What Are the Security Risks of Cloud Computing?
Cloud computing has transformed the way businesses operate, store data, and deploy applications. With benefits like cost efficiency, scalability, and global accessibility, organizations across all industries are rapidly migrating to cloud-based environments. However, despite its advantages, cloud computing introduces a range of security risks that must be understood and managed effectively.
This article provides a detailed exploration of what the security risks of cloud computing are, why they matter, and how businesses can mitigate them. Designed in an academic yet easy-to-understand style, it helps IT professionals, cloud architects, and decision-makers strengthen their cloud security posture.
What Are the Security Risks of Cloud Computing
Why Cloud Security Risks Matter
As organizations transition their workloads to the cloud, the traditional security model changes dramatically. Instead of hosting resources on-premises, where full control is maintained, businesses rely on third-party service providers such as Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform (GCP), and others. This shift creates new vulnerabilities, including shared responsibility concerns, external threats, data loss, account breaches, and misconfigurations.
Understanding these risks is the first step toward designing a secure, compliant, and resilient cloud environment.
What Are the Security Risks of Cloud Computing
1. Data Breaches
A data breach is one of the most severe cloud security risks. It occurs when unauthorized individuals gain access to sensitive information such as customer data, financial records, intellectual property, or confidential communication.
Why Data Breaches Happen in the Cloud
Weak authentication or compromised credentials
Misconfigured storage buckets
Vulnerable APIs
Inadequate encryption
Insider threats
Consequences
Financial losses
Reputational damage
Legal penalties
Loss of customer trust
Solutions include multi-factor authentication (MFA), encryption at rest and in transit, access control policies, and continuous security monitoring.
What Are the Security Risks of Cloud Computing
2. Misconfigured Cloud Settings
One of the most common cloud security risks is misconfiguration, which happens when cloud resources such as storage, virtual machines, or security groups are set up incorrectly.
Examples of Misconfigurations
Publicly exposed storage buckets
Open ports on virtual machines
Incorrect IAM permissions
Disabled logging or monitoring
Why Misconfiguration Is Dangerous
Cybercriminals actively scan the internet for misconfigured cloud assets. Even a simple error—such as making a storage bucket public—can expose millions of records.
To prevent this, organizations should use configuration management tools, adopt the principle of least privilege, and conduct continuous audits.
What Are the Security Risks of Cloud Computing
3. Insecure APIs and Interfaces
Cloud environments rely heavily on APIs (Application Programming Interfaces) for managing resources. If these interfaces are insecure, attackers can exploit them to access or modify cloud data.
Common API Risks
Weak authentication
Lack of input validation
Excessive permissions
Outdated API versions
Poor endpoint security
How to Mitigate API Risks
Use OAuth, token-based authentication, and MFA
Apply strict API gateway policies
Limit API rate usage
Enable logging and monitoring
APIs are powerful, but they must be secured as they are often the first target in cloud attacks.
What Are the Security Risks of Cloud Computing
4. Account Hijacking
Account hijacking occurs when attackers steal cloud account credentials, allowing them to manipulate resources, steal data, or deploy malicious applications.
How Attackers Hijack Accounts
Phishing attacks
Password reuse
Weak passwords
Social engineering
Credential stuffing attacks
Potential Damage
Unauthorized access to databases
Deletion of critical information
Deployment of crypto-mining malware
Manipulation of business operations
To prevent account hijacking, organizations should implement MFA, detect suspicious login patterns, enforce strong password policies, and rotate credentials regularly.
What Are the Security Risks of Cloud Computing
5. Insider Threats
Not all cloud risks come from outside the organization. Insider threats can be intentional or accidental and often involve employees, contractors, or third-party service providers.
Types of Insider Threats
Malicious insiders seeking financial gain
Negligent employees causing accidental exposure
Abused privileged access
Why Insider Threats Are Dangerous
Insiders already have access to internal systems, making it difficult to detect unusual behavior.
Mitigation strategies include role-based access control (RBAC), real-time monitoring, user behavior analytics (UBA), and zero-trust principles.
What Are the Security Risks of Cloud Computing
6. Limited Visibility and Control
When using the cloud, organizations may lose some visibility and control over their infrastructure. Since cloud resources are managed by external providers, businesses cannot always monitor hardware or lower-level components.
Challenges Due to Limited Visibility
Difficulty detecting unusual activities
Inability to monitor all layers of the infrastructure
Blind spots in network traffic
Limited access to logs or performance metrics
How to Improve Visibility
Implement cloud-native monitoring tools
Use SIEM (Security Information and Event Management) systems
Set up unified dashboards for multi-cloud environments
Visibility is key to maintaining a strong security posture in the cloud.
What Are the Security Risks of Cloud Computing
7. Data Loss and Inadequate Backups
Data stored in the cloud can be lost due to human error, cyberattacks, provider outages, or accidental deletion.
Causes of Cloud Data Loss
Ransomware attacks
Misconfiguration
Accidental deletion
Application failures
Provider outages
Prevention Strategies
Automated backups
Multi-region replication
Versioning policies
Disaster recovery planning
Cloud providers are responsible for infrastructure availability, but the customer must protect the data itself.
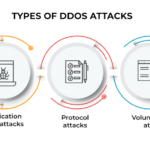
8. Denial of Service (DoS) and Distributed DoS (DDoS) Attacks
DoS and DDoS attacks overwhelm cloud services with massive traffic, causing downtime and making applications inaccessible.
Why Cloud Environments Are Targeted
Cloud workloads are internet-facing
Attackers exploit weak configuration
Easy to overload small cloud instances
Impact of DDoS Attacks
Service disruption
Financial losses
User dissatisfaction
Potential cascading failures
Cloud providers offer DDoS protection tools, but organizations must implement rate limiting, auto-scaling, and network security measures.
What Are the Security Risks of Cloud Computing
9. Compliance and Legal Risks
Many industries must comply with strict regulations such as:
GDPR
HIPAA
PCI DSS
ISO 27001
Storing data in the cloud without understanding regional laws may lead to fines and sanctions.
Key Risks
Storing data in non-approved regions
Improper handling of personal data
Failure to meet audit requirements
To avoid these issues, businesses must choose cloud providers with strong compliance portfolios and ensure internal policies align with legal obligations.
What Are the Security Risks of Cloud Computing
10. Shadow IT in Cloud Environments
Shadow IT refers to employees using unauthorized cloud services without the knowledge of the IT department.
Why Shadow IT Is Dangerous
No official security controls
No visibility into data usage
High risk of accidental exposure
Inconsistent compliance
Organizations must implement clear cloud usage policies, monitoring tools, and employee training programs.
What Are the Security Risks of Cloud Computing
11. Multi-Cloud and Hybrid Cloud Complexity
Using multiple cloud providers or combining cloud with on-premises systems increases complexity, making it harder to secure the environment.
Key Risks
Configuration inconsistencies
Difficulty managing identities across platforms
Multiple security tools and dashboards
Higher attack surface
Unified security management tools and zero-trust architecture help reduce these risks.
What Are the Security Risks of Cloud Computing
Best Practices to Mitigate Cloud Security Risks
To reduce cloud risks, organizations should:
1. Apply the Shared Responsibility Model
Understand which security tasks belong to the provider and which belong to the customer.
2. Use Strong Authentication
Enable MFA, rotate credentials, and implement IAM policies.
3. Encrypt All Data
Encryption at rest and in transit is essential.
4. Conduct Regular Audits
Routine security audits detect misconfigurations early.
5. Implement Zero-Trust Architecture
Assume no device or user is trustworthy by default.
6. Use Cloud-Native Security Tools
Such as AWS GuardDuty, Azure Security Center, and Google Cloud Armor.
What Are the Security Risks of Cloud Computing
Conclusion
Understanding what the security risks of cloud computing are is essential for building a secure and resilient cloud environment. While cloud technology offers powerful benefits—scalability, flexibility, and cost savings—it also introduces unique vulnerabilities such as data breaches, misconfigurations, insecure APIs, insider threats, and limited visibility.
By adopting strong security practices, leveraging cloud-native tools, and understanding the shared responsibility model, organizations can minimize risks and confidently embrace cloud computing.